8. Technology development (Tools Git, ngrok)¶
Technology Development - includes research and development, process automation, and other technology development used to support the value-chain activities.
8.1. The digitization¶
The Digitization is “Digitization, less commonly digitalization, is the process of converting information into a digital (i.e. computer-readable) format, in which the information is organized into bits.”
In short, developing software mimicking manual processes while adding new capabilities such enabling the communication between IT systems from different companies that couldn’t have been integrated using another way.
8.1.1. Digitization for the Insurance industry¶
8.1.1.1. Presentation layer I¶
The presentation layer is the layer that is in connection with your customers through several means or devices :
8.1.1.1.1. Telephone¶
A service desk supporting the requests on the phone
8.1.1.1.2. Robo advisor¶
A Robo advisor is a class of financial adviser that provide financial advice or Investment management online with moderate to minimal human intervention
The Robo advisor scans and dematerializes your documents
The Robo advisor compares the available offers and optimize the portfolio of your customers
The customer interacts with the trusted Robo advisors via the web, mobile chat or email
8.1.1.1.3. Mobile or Smartphone¶
Mobile phones accessing the insurer’ services through SMS, email, voice of mobile app means
8.1.1.1.4. SMS¶
The customer interacts with the Insurer using SMS. The answers to the SMS are made by a Robo advisor, a Chatbot or a human. The help desks uses an IT system and (s)he is not necessarily answering using a mobile phone.
8.1.1.1.5. Web Browser¶
a software used to access the Web site of the insurer or the Underwriter (i.e. Firefox, Opera, Ecosia, Microsoft Internet Explorer, Google Chrome, Microsoft Edge, Safari)
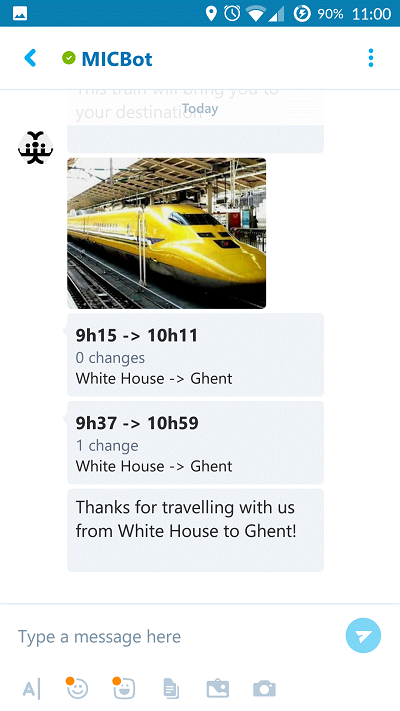
8.1.1.1.6. Chatbot¶
The Chatbot is a piece of software that conducts a conversation via auditory or textual methods.
The Chatbot tries to answer customers’ questions that human would have had as a conversation. Some chatbots use sophisticated natural language processing systems but are most of time supported by a service desk run by humans when the Chatbot can’t understand the demands made by the customer.
8.1.1.2. Presentation layer II¶
The presentation layer counts the front office as well as the back office. The Back office is all the resources of the company that are devoted to actually producing a product or service and all the other labor that isn’t seen by customers, such as administration or logistics.
8.1.1.2.1. Back office workstation¶
Those are the collaborators managing the operations ensuring the correct exection of the processes :
quote an offer
validate personal data
validate the filling of a form
perform the dunning services duties
The back office requires documentation, software and reports to perform their duties.
8.1.1.2.2. Middle office workstation¶
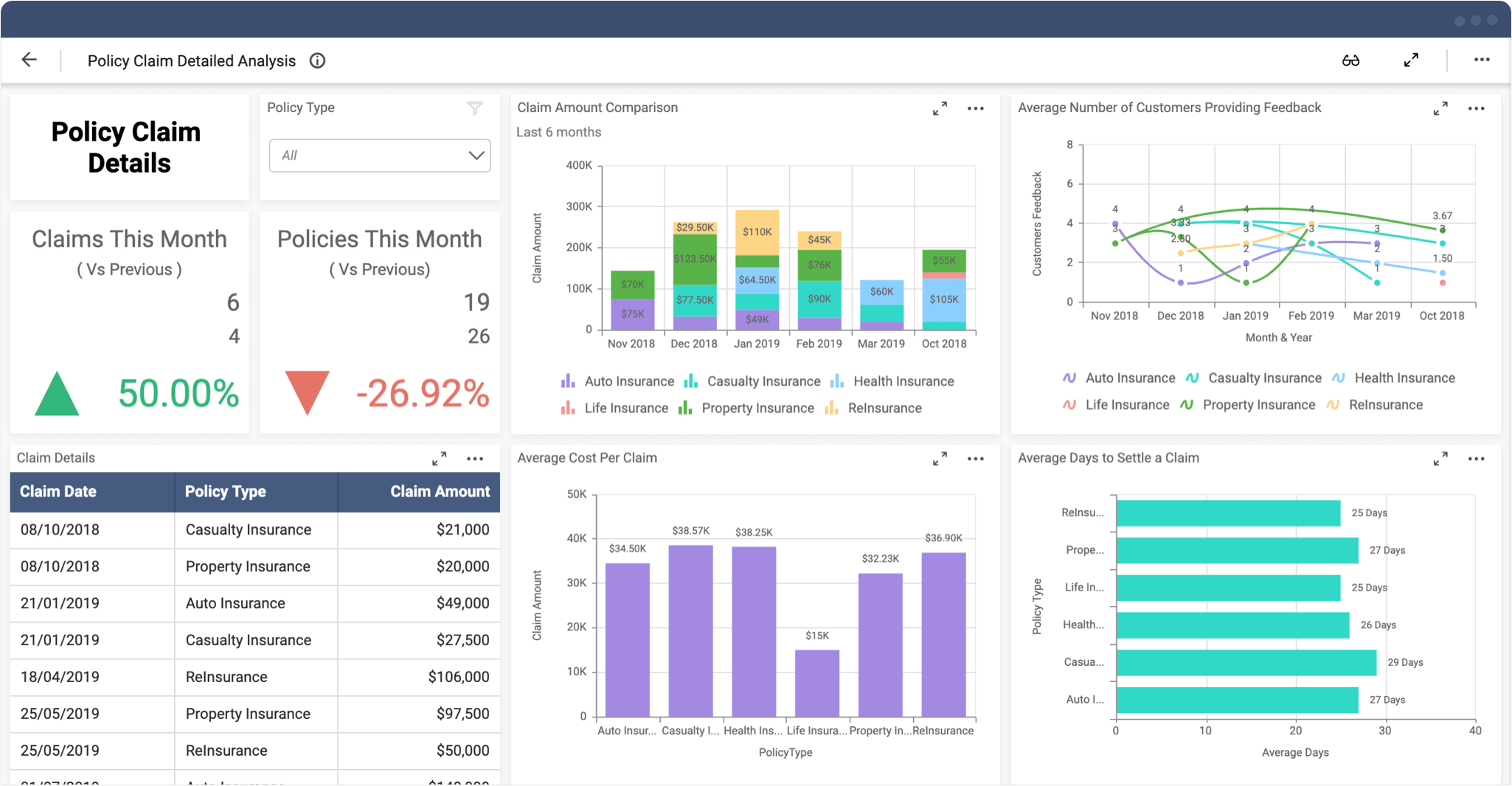
The Middle office is made up of the risk managers and the information technology managers who manage risk and maintain the information resources.
Track claim settlement times
Customer satisfation ratings
Long-term trends in customer activity
Data collected during the operations are stored into IT systems operated by a multitude of managers (risks, operations, HR, Marketing)
Those data are analysed and supports the value chain (logistics, operations, marketing, sales, support) by giving a broad and exact view of the financial situation of the company.
After a careful analysis, the data are shared with the back office who can act and interact with prospects, customers and suppliers depending on the situation (dunning service, quotation, billing, closing off the contract)
Tip
Try the Insurance claims analysis dashboard
8.1.1.2.3. Call centre¶
Three types of call centres might be operated by a financial service company:
An Inbound call center is operated by a company to administer incoming product or service support or information enquiries from consumers.
An Outbound call center is operated for telemarketing, for solicitation of charitable or political donations, debt collection, market research, emergency notifications, and urgent/critical needs blood banks.
A Contact center, further extension to call centers administers centralized handling of individual communications, including letters, faxes, live support software, social media, instant message, and e-mail.
8.1.1.2.4. Customer portal¶
A website accessible through a Web browser or a mobile phone enabling the customer to access all the aspects of his duties and rights towards the insurer.
The portal gives access to diverse functionalities:
Information platform: share details about the products and services, how to contact the insurer
Transaction platform: create, update or delete information, stop a current insurance, pay electronically the remaining Bills
Sales platform: generate up-sell and cross-sell opportunities, promote the Robo advisor capabilities
Rewards platform: Insurers retain their customers through the Perceived Value of the customer, the Affinity that the customer has with his insurer, and the Barriers to Exit
Perceived value: does the customer feels that (s)he has coverage at a competitive and fair price?
Affinity: do the customer has a emotional connection with the customer? Insurance products may tend to have a limited value due to the commoditized nature of the product
Barriers to Exit: does the customer has strong and effective reasons to do not leave an insurer? the lack of competition, the increase of costs, the loss of a unique protection, a decrease of the quality of service
8.1.1.2.5. Broker portal¶
A broker portal is a website enabling the Broker to perform her/his duties
Information platform: share details about the products and services, how to contact the insurer, the customers
Sales platform: support the sales process (from a quote to a signed contract), generate up-sell and cross-sell opportunities
Marketing platform: identify new sales opportunites by advertising the products and identify the most profitable or potential prospects
CRM platform: maintain data related to the prospects and customers (contact details, online and offline interactions)
Dunning service platform: inform and give the tools to enable the broker to run after unpaid invoices till the termination of the contract
8.1.1.3. Business logic tier I¶
8.1.1.3.1. API Gateway¶
The API describes the functions or the interfaces available between a client and a server.
APIs are enablers of the platform economy, and allow users to enhance and add services over existing products.
For example: An API enables an application ‘A’ to query a system ‘B’ and collects the schedule of the public transportation (See https://opendata.stib-mivb.be/store/data)
Tip
Look at the description of the API from a dunning Service https://dunningcashflow-api.azurewebsites.net/swagger/index.html
8.1.1.4. Business logic tier II¶
8.1.1.4.1. Business Risk Management¶
The financial services must comply with a multitude of risks.
Here are a list of pure risks (loss or no loss only) that an insurer or a Underwriter may be confronted with:
Regulatory Compliance: Invoice compliance, MiFID ii, MiFID 2, Solvency II, Solvency 2
Tax Compliance: Tax determination, Fiscal reporting, VAT reporting
Liability risk exposure: product liability risks, or contractual liability risks
Operational risk: mistakes in process and procedure
Intellectual property violation risk
Mortality and morbidity risk at the societal and global level
Warning
Speculative risks are not described in this documents. i.e. market risk, reputational risk, brand risk, product success risk…
8.1.1.4.2. Business Process Management¶
The Business Process Management is a discipline aimed at managing all aspect of the business processes; from process design to modeling and analysis to execution and improvement.
Note
Here is the description of a process: Data entry of a claim
8.1.1.5. Business logic tier III¶
8.1.1.5.1. Finance management¶
8.1.1.5.2. Customer management¶
8.1.1.5.3. Claims management¶
8.1.1.5.4. Product management¶
8.1.1.5.5. Policy management¶
8.1.1.6. Business logic tier IV¶
8.1.1.6.1. Customers¶
8.1.1.6.2. Claims¶
8.1.1.6.3. Products¶
8.1.1.6.4. Policies¶
8.1.1.6.5. Entreprise services¶
8.1.1.6.6. Quotes¶
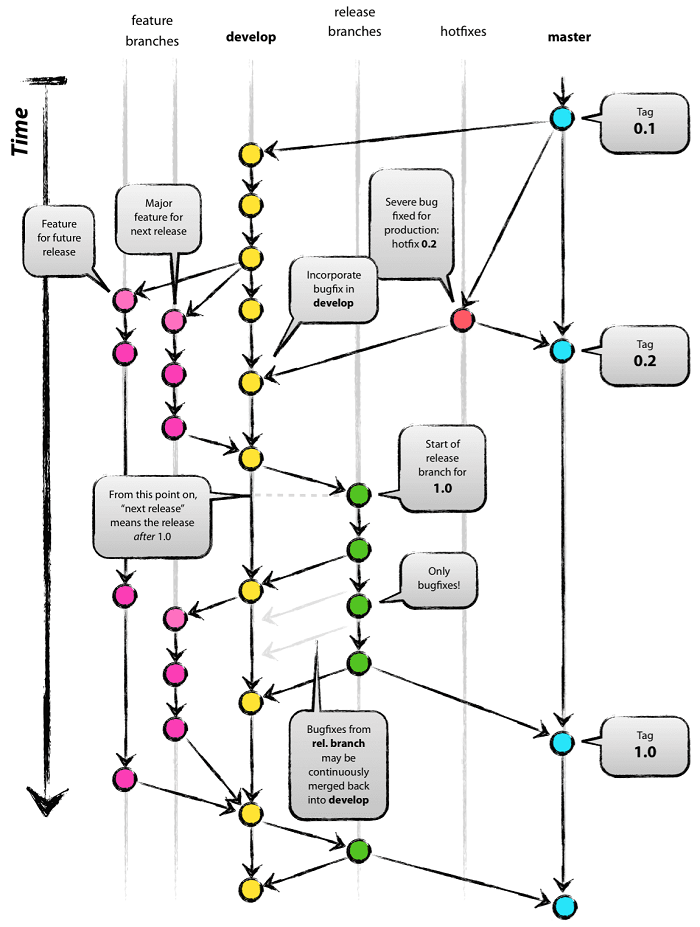
8.2. GIT lifecycle¶
Description of how to manage the versions, branches in a git repository as well the operations of the software
How to write relevant commits?
8.2.1. A successful git branching model¶
A successful Git branching model : https://nvie.com/posts/a-successful-git-branching-model/
8.2.2. GIT : commit conventions¶
source : conventional commits : https://github.com/conventional-commits
Semantic messages: http://seesparkbox.com/foundry/semantic_commit_messages
build
chore (maintain i.e. updating grunt tasks etc; no production code change)
ci (continuous integration)
docs (documentation)
feat (feature)
fix (bug fix)
perf (performance improvements)
refactor (refactoring production code)
revert
style (formatting, missing semi colons, …)
test (adding missing tests, refactoring tests; no production code change)
enumeration : https://github.com/conventional-changelog/commitlint/tree/master/%40commitlint/config-conventional#type-enum
Install commitlint : https://conventional-changelog.github.io/commitlint/#/
8.2.2.1. Example of commits¶
Source : https://github.com/conventional-commits/conventionalcommits.org/commits/master
8.2.3. GIT : how to manage the versions, branches … ?¶
GIT : Create a branch : [BRANCH-DEV] – [BRANCH-PARENT]
DEV : Local development on Software engineer machine
MERGE GIT : Merge the [BRANCH-DEV] with the [BRANCH-PARENT]
The code is merged into the [BRANCH-DEV]
STAGING : The Software is deployed on the staging environment
MERGE GIT : Merge the [BRANCH-DEV] with the [BRANCH-PARENT]
The code is merged into the [BRANCH-PARENT]
PROD : Test the PROD version of the software
LIVE : deploy the PROD version of the software on the PROD server
8.2.4. GIT LFS Large File System¶
git commands
Install git lfs https://git-lfs.github.com
- Locks
git lfs lock images/foo.jpg
git lfs locks
git lfs unlock images/foo.jpg
git lfs push origin master –all
8.2.4.1. Create a .gitattributes file¶
.. include:: .gitattributes
8.2.4.2. Commands to add files into the repository, and push the code¶
git lfs install
git lfs track "*.jpg" --lockable
git lfs track "*.JPG" --lockable
git lfs track "*.png" --lockable
git lfs track "*.zip" --lockable
git lfs track "*.mp4" --lockable
git lfs track "*.MP4" --lockable
git lfs track "*.docx" --lockable
git lfs track "*.svg" --lockable
git lfs track "*.gif" --lockable
git lfs track "*.psd" --lockable
git lfs track "*.sketch" --lockable
git lfs track "*.ai" --lockable
git add "*.jpg" "*.JPG" "*.png" "*.zip" "*.mp4" "*.MP4" "*.docx" "*.svg" "*.gif"
git lfs ls-files
git lfs env
git config lfs.https://inlsprl.visualstudio.com/[ProjectName]/_git/[ProjectName].git/info/lfs.locksverify true
git push origin master
git lfs push origin master --all
8.3. ngrok - Public URLs for exposing your local web server¶
Use ngrok to grant access to your localhost to anyone
Install https://ngrok.com/download
open the port where the web server is located. run the following command :
[path to ngrok]\ngrok.exe http [port to open on your localhost] -host-header=rewrite
share the URL to the person who needs to access your local machine. i.e. https://a1cc816e.ngrok.io
ngrok by @inconshreveable
Session Status online Account [the account name] (Plan: Free) Update update available (version 2.2.8, Ctrl-U to update) Version 2.2.3
Region United States (us) Web Interface http://127.0.0.1:4040
Forwarding http://a1cc816e.ngrok.io -> localhost:4624 Forwarding
https://a1cc816e.ngrok.io -> localhost:4624
8.4. How to write a bug report?¶
Copy paste the content hereunder
Create a new issue: https://bitbucket.org/altf1be/software-architecture/issues/new
## WHAT STEPS WILL REPRODUCE THE PROBLEM?
1. Open the page
2.
3.
## WHAT IS THE EXPECTED OUTPUT?
* StratEx is loaded
## WHAT DO YOU SEE INSTEAD?
* The screenshot attached to this email
* StratEx cannot be opened because of a problem
## WHAT VERSION OF THE PRODUCT ARE YOU USING?
* Version: 3.5.6245.20028
* on [https://www.stratexapp.com](https://www.stratexapp.com)
* on [https://staging.stratexapp.com](https://staging.stratexapp.com)
* on [https://develop.stratexapp.com](https://develop.stratexapp.com)
## ON WHAT OPERATING SYSTEM, BROWSER, ETC.?
* Windows 7.1
* Chrome Version 54
* Internet Explorer 11
* Opera Version 41
* Windows 10
* Internet Explorer
* Edge
* Mac OS X 10.9 (13A603)
* Safari Version 7.0 (9537.71)
* Chrome Version 31.0.1650.57
## PLEASE PROVIDE ANY ADDITIONAL INFORMATION BELOW.
* None
* Extra files are available on [StratExApp files on Google Drive]
* Find the private [Videos generated on GDrive]
* Find the public [Videos on StratEx YouTube channel]
* Find the public [Documentation on Read The Docs]
## Bug report (if any)
* None
[StratExApp files on Google Drive]: https://drive.google.com/a/alt-f1.be/folderview?id=0B9L2cx0TUjLGUFZBSkF6WlFCYms&usp=sharing#list
[Videos generated on GDrive]: https://drive.google.com/a/alt-f1.be/folderview?id=0B9L2cx0TUjLGa190N1ZURHBpUFE&usp=sharing
[Videos on StratEx YouTube channel]: https://www.youtube.com/channel/UCuwGfoVoozq0ZTmHJ3WCvTQ
[Documentation on Read The Docs]: http://stratexapp-docs.readthedocs.org/en/latest/
8.5. Research & Development topics¶
Prerequisite:
Use Technologies supported by Microsoft
ASP.NET Core - https://docs.microsoft.com/en-us/aspnet/core/
Microsoft Azure: https://portal.azure.com
Single Page Application (SPA)
Build a SPA such as Microsoft Azure for our customers
Test SPA App
IT Automation best practices
Reading : https://www.joelonsoftware.com/2000/08/09/the-joel-test-12-steps-to-better-code/
In general we should go for 1-click test/deployment
Design
Development
Test (SPA, Web apps)
Unit
UAT (user acceptance test)
Deployment
Documentation
Design
Code
User manual
Security
8.6. Open Authentication (OAuth)¶
OAuth is an open standard for access delegation, commonly used as a way for Internet users to grant websites or applications access to their information on other websites but without giving them the passwords.
Source: Wikipedia contributors. (2019, March 19). OAuth. In Wikipedia, The Free Encyclopedia. Retrieved 12:20, March 23, 2019, from https://en.wikipedia.org/w/index.php?title=OAuth&oldid=888559139
8.6.1. Use case for Open Authentication¶
A user requires access to a resource on a web application (eg StratEx) using her credentials from another website (eg Microsoft Office365).
She needs to login using the form from Office365
Office365 will generate a token
The token is used by StratEx ensuring that the user is effectively logged using her Office365 credentials
StratEx can use the resources made available by Office365 such as username, firstname, lastname, email address, read access to OneDrive, write and send new emails…
8.6.2. Open authentication using Office365¶
Microsoft graph documentation makes available Office365 resources of each registrered user:
Request an access token to Office 365:
Description of each parameter (see use-the-authorization-code-to-request-an-access-token):
https://login.microsoftonline.com/common/oauth2/v2.0/authorize
? client_id =f5d835b0-4bc1-98e7-f98cb4aaef31
& scope =https%3A%2F%2Fgraph.microsoft.com%2Fuser.read
& response_type =code
& redirect_uri =https%3A%2F%2Ftimesheet-stg-inlsprl.azurewebsites.net%2Fsignin-microsoft
& state =Ao8m01yi1E76wQIXPJW-F92Fq1v
8.7. Web Scraping¶
8.7.1. Documentation¶
https://delftswa.gitbooks.io/desosa-2017/content/scrapy/chapter.html, Joren Hammudoglu (@jorenham), Johan Jonasson (@jojona), Marnix de Graaf (@Eauwzeauw)
8.7.2. Scraping: Software architecture¶
8.7.3. Scraping: best practices¶
8.7.4. Extraordinary examples¶
How To Scrape Amazon Product Data and Prices using Python 3
8.7.4.1. selectors.yml¶
name:
css: '#productTitle'
type: Text
price:
css: '#price_inside_buybox'
type: Text
short_description:
css: '#featurebullets_feature_div'
type: Text
images:
css: '.imgTagWrapper img'
type: Attribute
attribute: data-a-dynamic-image
rating:
css: span.arp-rating-out-of-text
type: Text
number_of_reviews:
css: 'a.a-link-normal h2'
type: Text
variants:
css: 'form.a-section li'
multiple: true
type: Text
children:
name:
css: ""
type: Attribute
attribute: title
asin:
css: ""
type: Attribute
attribute: data-defaultasin
product_description:
css: '#productDescription'
type: Text
sales_rank:
css: 'li#SalesRank'
type: Text
link_to_all_reviews:
css: 'div.card-padding a.a-link-emphasis'
type: Link
8.7.4.2. Amazon.py¶
from selectorlib import Extractor
import requests
import json
from time import sleep
# Create an Extractor by reading from the YAML file
e = Extractor.from_yaml_file('selectors.yml')
def scrape(url):
headers = {
'authority': 'www.amazon.com',
'pragma': 'no-cache',
'cache-control': 'no-cache',
'dnt': '1',
'upgrade-insecure-requests': '1',
'user-agent': 'Mozilla/5.0 (X11; CrOS x86_64 8172.45.0) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/51.0.2704.64 Safari/537.36',
'accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9',
'sec-fetch-site': 'none',
'sec-fetch-mode': 'navigate',
'sec-fetch-dest': 'document',
'accept-language': 'en-GB,en-US;q=0.9,en;q=0.8',
}
# Download the page using requests
print("Downloading %s"%url)
r = requests.get(url, headers=headers)
# Simple check to check if page was blocked (Usually 503)
if r.status_code > 500:
if "To discuss automated access to Amazon data please contact" in r.text:
print("Page %s was blocked by Amazon. Please try using better proxies\n"%url)
else:
print("Page %s must have been blocked by Amazon as the status code was %d"%(url,r.status_code))
return None
# Pass the HTML of the page and create
return e.extract(r.text)
# product_data = []
with open("urls.txt",'r') as urllist, open('output.jsonl','w') as outfile:
for url in urllist.readlines():
data = scrape(url)
if data:
json.dump(data,outfile)
outfile.write("\n")
# sleep(5)
8.7.5. Data model of a scraper¶
8.7.6. Scraping: Scrapy spiders or Crawlers¶
8.7.7. Similarity features¶
Jaccard: https://en.wikipedia.org/wiki/Jaccard_index
TD-IDF, term frequency–inverse document frequency: https://en.wikipedia.org/wiki/Tf%E2%80%93idf
Mann–Whitney U test is a nonparametric test of the null hypothesis that, for randomly selected values X and Y from two populations, the probability of X being greater than Y is equal to the probability of Y being greater than X.
Kolmogorov–Smirnov test In statistics, the Kolmogorov–Smirnov test (K–S test or KS test) is a nonparametric test of the equality of continuous (or discontinuous, see Section 2.2), one-dimensional probability distributions that can be used to compare a sample with a reference probability distribution (one-sample K–S test), or to compare two samples (two-sample K–S test).
Source : AAAI 2018 Tutorial Building Knowledge Graphs
8.8. Authentic sources¶
Een authentieke bron is een gegevensbank waarin authentieke gegevens worden bewaard en die geldt als dé referentie voor deze specifieke gegevens over personen en rechtsfeiten. Bron: https://dt.bosa.be/nl/authentieke_bronnen
Une source authentique est une banque de données au sein de laquelle des données authentiques sont conservées et qui sert de référence pour ces données spécifiques sur des personnes et faits juridiques. Source: https://dt.bosa.be/fr/echange_de_donnees/sources_authentiques
8.8.1. Geography - Countries¶
Get information about countries via a RESTful API : https://restcountries.eu